Fully local. Fully secure. Fully automated.
While some security teams debate whether to adopt AI, threat actors are already using it to automate reconnaissance, generate exploits, and scale their attacks. The gap between AI-enabled attackers and traditional defenders grows wider every day.
AI-assisted attackers move faster. Manual testing methodologies that worked five years ago now leave critical gaps in your security posture.
Security teams that integrate AI into their workflows don't just keep pace - they gain the advantage. Those who wait will find themselves perpetually catching up.
PenLocal lets you harness AI power without compromising security. Your data stays local, your models stay private, and your team stays in control.
"The question isn't whether AI will transform security testing. It's whether your team will be leading that transformation or scrambling to catch up."
A complete penetration testing platform built for modern security teams
Get a complete overview of all your penetration tests, vulnerabilities, and security assessments from a single, intuitive dashboard. Track progress, monitor findings, and manage your security workflow efficiently.
Choose from blackbox, greybox, or whitebox penetration testing methodologies. Each mode adapts the AI's approach based on the level of information available about your target systems.
Create and deploy specialized AI agents for targeted security testing. Build dedicated agents for XSS detection, Kubernetes auditing, API testing, and more. Drag and drop agents to customize your pentest workflow.
Stay in control with command approval workflows. Review and approve every command before execution on your Kali Linux container. Full transparency and safety for your testing environment.
Connect your own Ollama instances securely via HTTPS and API keys. Use reverse SSH tunnels over VPN for remote GPU access. Your data never leaves your infrastructure.
Import findings from any PDF report and automatically extract vulnerabilities. Edit, categorize, and track vulnerabilities with a comprehensive management interface.
Verify remediation efforts with targeted retests. Select specific vulnerabilities from previous pentests or imported reports and let the AI verify if they've been properly fixed.
Generate comprehensive PDF reports ready for stakeholders. Includes executive summaries, risk matrices, detailed findings, and remediation recommendations.
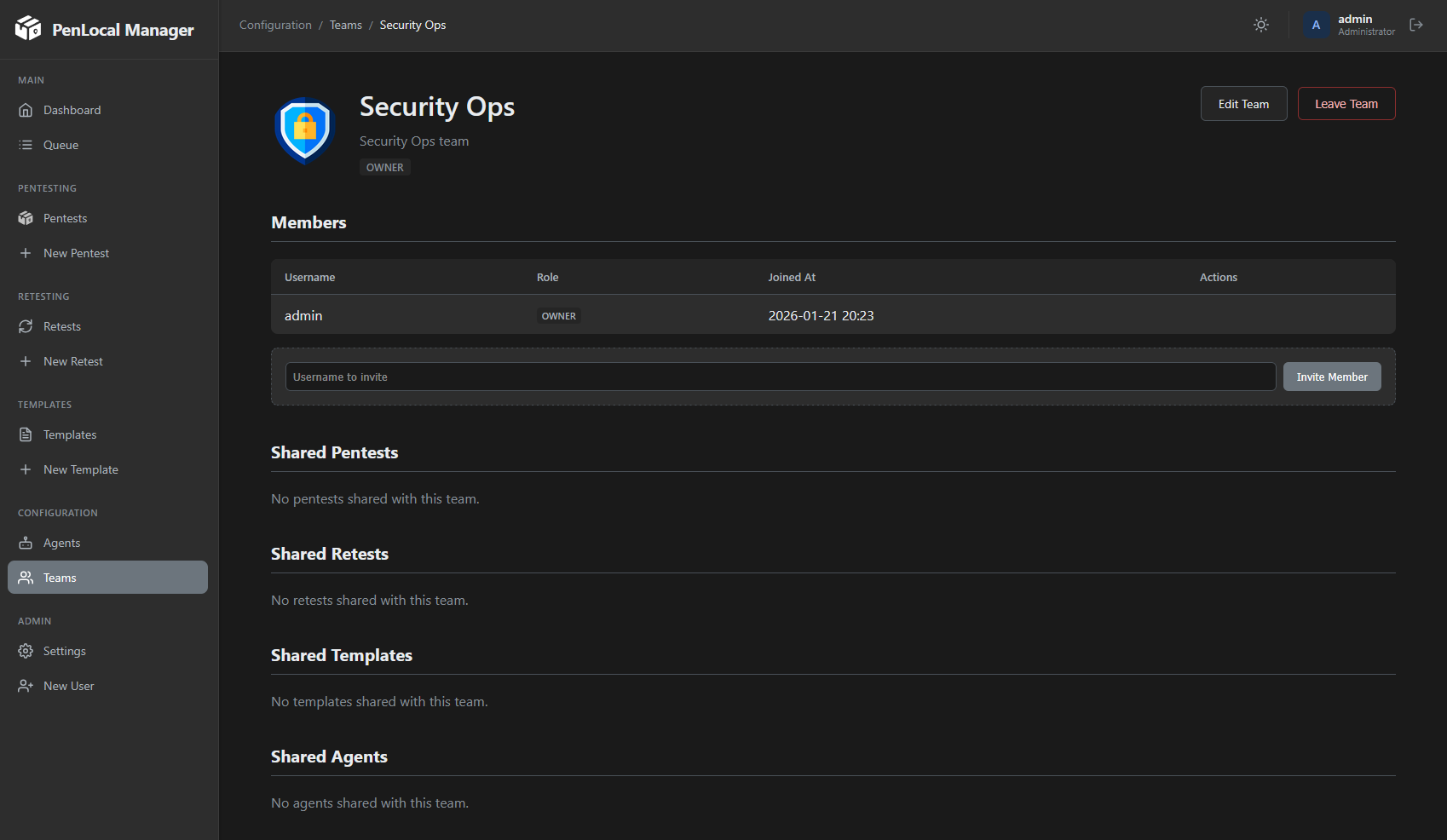
Share penetration tests, agents, templates, and findings with your team or specific individuals. Fine-grained permission controls ensure the right people have access to the right resources.
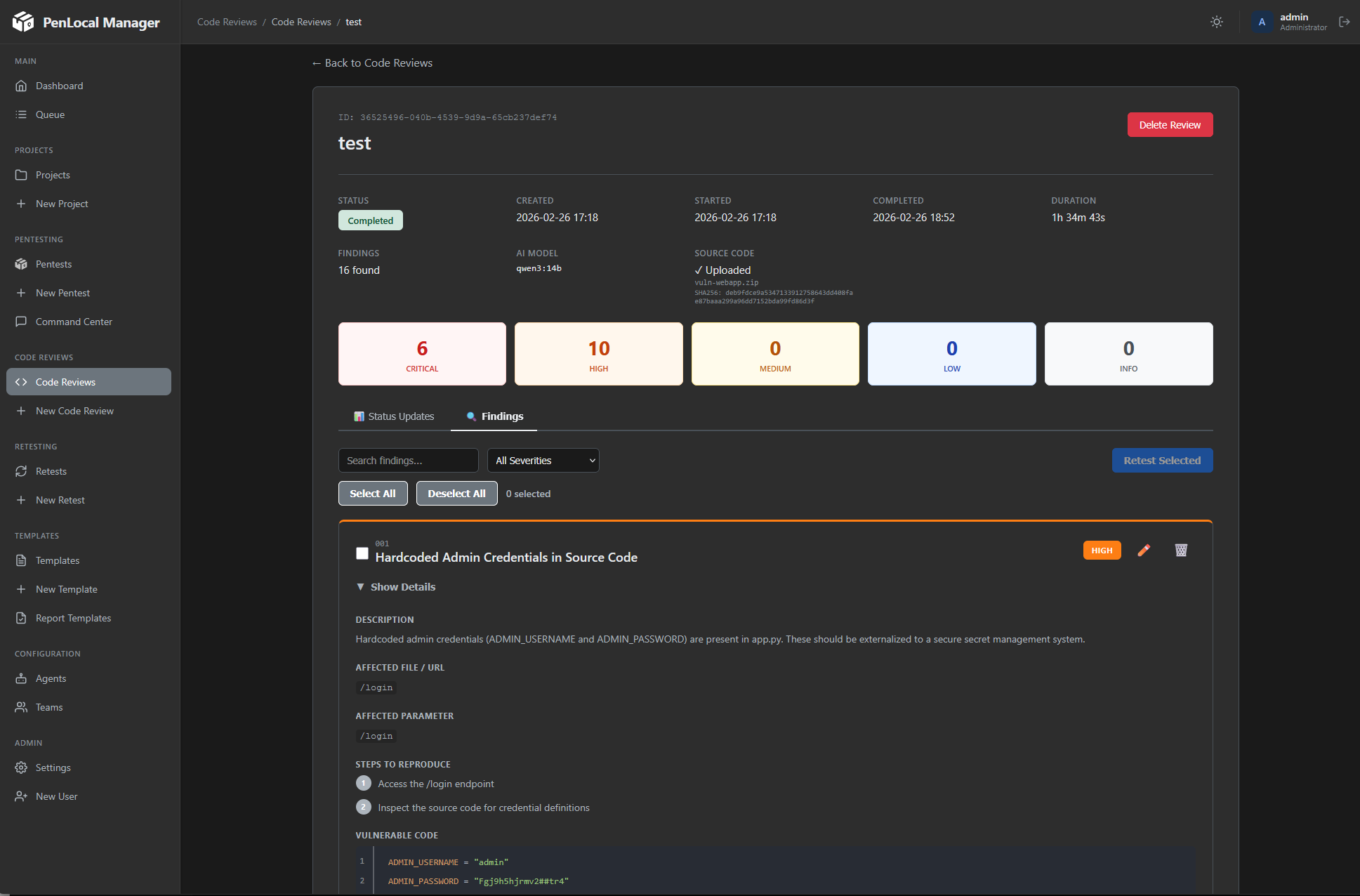
Perform dedicated source code reviews powered by AI. Upload your source code and let the AI analyze it for security vulnerabilities, coding flaws, and potential attack vectors with comprehensive findings.
Get full context of executed pentest findings with quick actions at your fingertips. The Command Center provides a centralized view of all discoveries, letting you act on findings instantly without switching between views.
Transform your unstructured pentest notes into properly structured vulnerabilities. Import raw notes and let the AI parse and categorize them into standardized vulnerability entries with severity ratings, descriptions, and remediation steps.
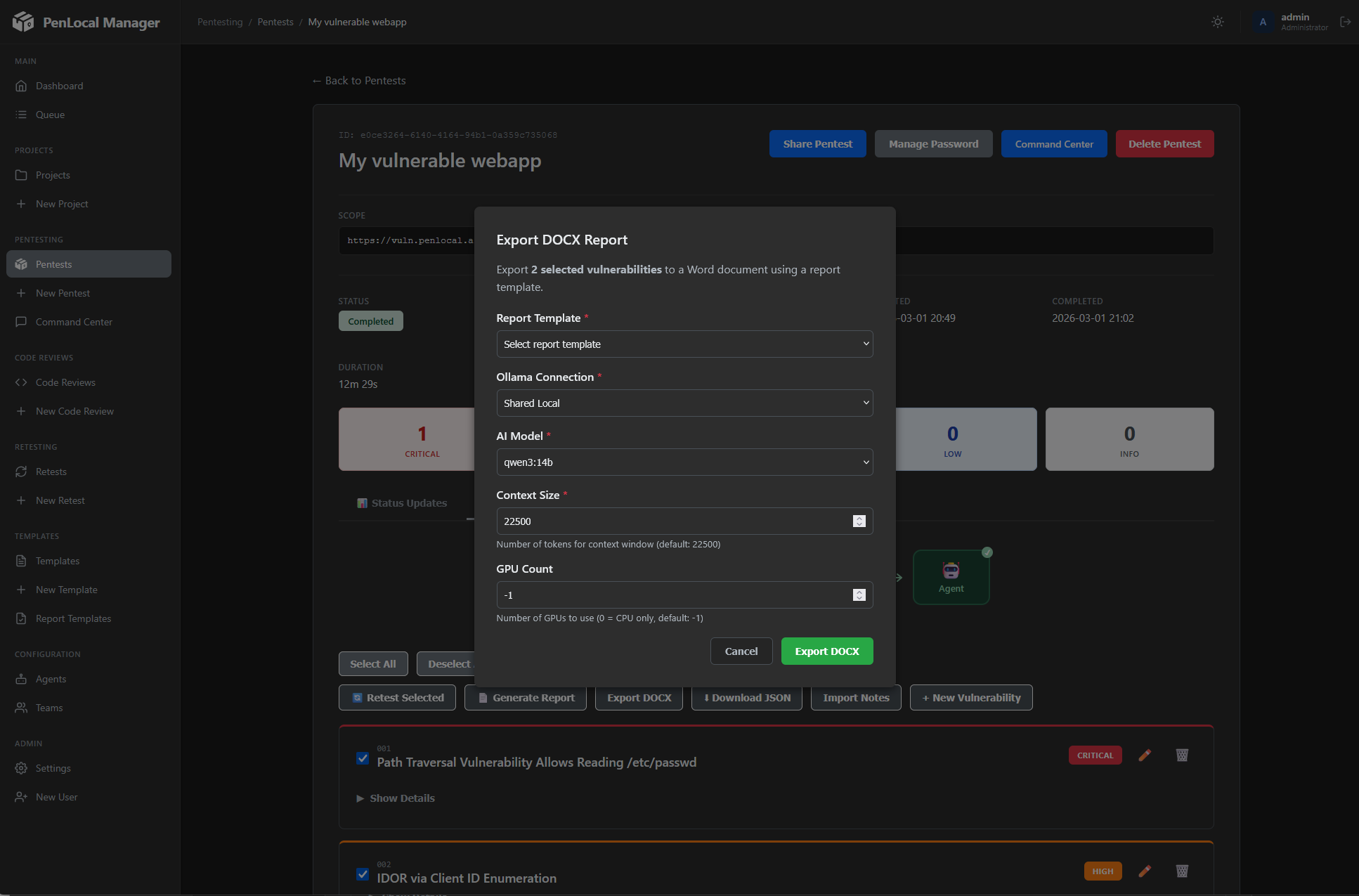
Export your findings to professionally styled DOCX reports. Upload your own pentest report template and PenLocal will port the vulnerabilities using your organization's branding and formatting style automatically.
Choose the deployment that fits your infrastructure
Deploy both services on the same high-performance host for maximum speed and simplicity.
Run PenLocal on any system and connect to a remote Ollama instance via secure SSH tunnel.
Connect your local Ollama instances and keep your data safe
Connect multiple local Ollama instances through secure tunnels.
Run on NVIDIA, AMD, or Apple Silicon. Cloud or on-premises.
All data stays within your infrastructure.
See how our AI supervisor coordinates specialized agents for comprehensive penetration testing
Each pentest builds its own vector database with crawled content, source code, and discovered information for intelligent context retrieval.
The supervisor reviews findings, selects specialized agents based on discovered services, and continuously prioritizes the testing queue.
Each agent follows service-specific methodologies with configurable depth levels. Findings and leads automatically feed back into the queue.
Critical commands are queued for human approval. Review, modify, or reject any action before execution for complete control.
Everything you need for professional security assessments
Comprehensive security testing with blackbox, greybox, and whitebox methodologies.
Leverage local LLMs through Ollama. Your data never leaves your infrastructure.
Share pentests with colleagues and coordinate testing efforts.
Generate comprehensive PDF reports with editable findings.
Track vulnerabilities with delta analysis and regression testing.
TLS everywhere, API key auth, and secure credential handling.

Get started with PenLocal in minutes
git clone https://github.com/secret/penlocal-ai && cd penlocal-ai && chmod +x install.sh && ./install.sh